Selepas terkena Smart HDD Virus, laptop saya terkena jangkitan TR/ATRAPS.Gen2 pula.
Saya terjumpa artikel di bawah. Tapi saya belum ikut lagi langkah2nya kerana saya mahu mencuba dengan SuperAntiSpyWare terlebih dahulu.
Setelah SuperAntiSpyWare menjalankan kerja-kerja nyah-virus dan laptop dihidupkan semula, Avira tetap mengeluarkan mesej tanda virus gagal dinyahkan seperti berikut:
Maknanya SuperAntiSpyWare pun tak mampu nak menentang TR/ATRAPS.Gen2
Seterusnya, saya cuba combofix pula (http://www.combofix.org/)
Lama juga Combofix bekerja. Laptop reboot dan Combofix terus bekerja dan memaparkan mesej melalui Tetingkap Konsol (Console Window). Akhirnya laptop reboot lagi sekali. Saya menunggu kalau-kalau Avira mengeluarkan mesej virus dikesan seperti di atas. Buat masa ini belum keluar.
Maka rumusannya, COMBOFIX adalah cara mudah untuk menyahkan TR/ATRAPS.Gen2!!
-------------------------------------------------------------------
How to Get Rid of TR/ATRAPS.Gen2 Completely – Remove TR/ATRAPS.Gen2 Manually
Avira keeps reporting TR/ATRAPS.Gen2 inside your computer? This virus always comes bundled with TR/Sirefef.AG.35 virus. Both of these Trojans are able to allow a remote attacker to gain control on the compromised computer. Remove it as quickly as you can once upon detection.
Once inside, it can deliver other malicious programs onto the infected computer system. Besides, it allows attackers to gain remote access and control to a victim’s PC, enabling them to steal any sensitive information such as passwords, usernames and login details found. Thus, your computer will be at risk and damaged easily. While you are surfing the web, it displays annoying ads and from that time, computer is slower and slower. That includes starting up, shutting down, playing games, and surfing the web. Therefore, you must remove such dangerous Trojan as soon as possible once found on your computer.
It prevents you from opening some application because the files are corrupted.
It can make your browser redirected to all kinds of malicious websites.
It is able to allow remote hacker access the compromised system for illicit purpose.
Note: TR/ATRAPS.Gen2 is a highly dangerous Trojan created by the internet hackers and infects your computer through vulnerability or security program exploits. Once found, an immediate removal is needed. You can chat with an expert now to further know about this virus.

From malicious drive-by-download scripts from corrupted porn and shareware / freeware websites.
Through spam email attachments, media downloads and social networks.
When clicking suspicious popups or malicious links.
Open unknown email or download media files that contain the activation code of the virus.
Note: No matter how does the virus access your PC, users should know that there are no tools can remove this virus automatically at this moment, it is suggested users not spend much time in downloading or paying any security software which claims can delete this stubborn virus. It is totally useless. To completely get rid of this pest, professional manual guide is needed.
2. Show hidden files and folders.
3. Open Registry entries. Find out the malicious files and entries and then delete all.
Attention: Always be sure to back up your PC before making any changes.
a. Press the “Start” button and then choose the option “Run”. In the “Open” field, type “regedit” and click the “OK” button.
b. All malicious files and registry entries that should be deleted:
%System%\drivers\[RANDOM CHARACTERS].sys
%Temp%\[random]
C:\WINDOWS\system32\[random name].dll
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer “NoDesktop” = ’1?
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableTaskMgr” = ’1?
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “[random].exe”
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “[random]”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “DisableTaskMgr” = ’1?
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download “CheckExeSignatures” = ‘no’
Manual removal of TR/ATRAPS.Gen2 requires Expertise, Please take care before performing the steps.
TR/ATRAPS.Gen2 Description
TR/ATRAPS.Gen2 is classified as a nasty Trojan infection that can penetrate into the corrupted PC without the computer user’s consent and awareness. After accessing the target computer, it disguises itself in Windows directory folder named System32 or System64 based on the type of the OS so that it is difficult for user to detect or remove this pesky Trojan by the current security tools. Most of time, users can discover this trojan by running Avira Antivirus, however, it can’t help to delete TR/ATRAPS.Gen2 completely as the virus always comes back again and again after each time rebooting the machine. Without a doubt, this trojan is a disaster for all the computers.Once inside, it can deliver other malicious programs onto the infected computer system. Besides, it allows attackers to gain remote access and control to a victim’s PC, enabling them to steal any sensitive information such as passwords, usernames and login details found. Thus, your computer will be at risk and damaged easily. While you are surfing the web, it displays annoying ads and from that time, computer is slower and slower. That includes starting up, shutting down, playing games, and surfing the web. Therefore, you must remove such dangerous Trojan as soon as possible once found on your computer.
Trojan infected symptoms:
It can bypass the legit security tools and destroy your computer secretly.It prevents you from opening some application because the files are corrupted.
It can make your browser redirected to all kinds of malicious websites.
It is able to allow remote hacker access the compromised system for illicit purpose.
Note: TR/ATRAPS.Gen2 is a highly dangerous Trojan created by the internet hackers and infects your computer through vulnerability or security program exploits. Once found, an immediate removal is needed. You can chat with an expert now to further know about this virus.

Cause:
TR/ATRAPS.Gen2 can infect via many ways:From malicious drive-by-download scripts from corrupted porn and shareware / freeware websites.
Through spam email attachments, media downloads and social networks.
When clicking suspicious popups or malicious links.
Open unknown email or download media files that contain the activation code of the virus.
Note: No matter how does the virus access your PC, users should know that there are no tools can remove this virus automatically at this moment, it is suggested users not spend much time in downloading or paying any security software which claims can delete this stubborn virus. It is totally useless. To completely get rid of this pest, professional manual guide is needed.
Manual Removal Guides:
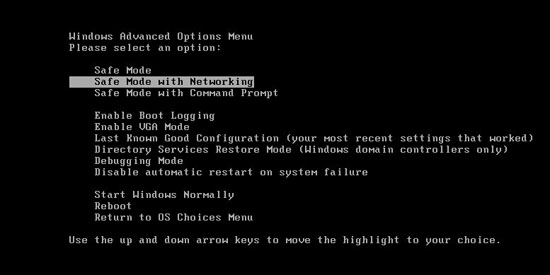
1. Reboot your computer to safe mode with networking. As your computer restarts but before Windows launches, tap “F8″ key constantly.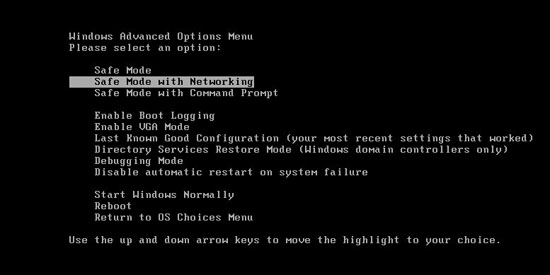
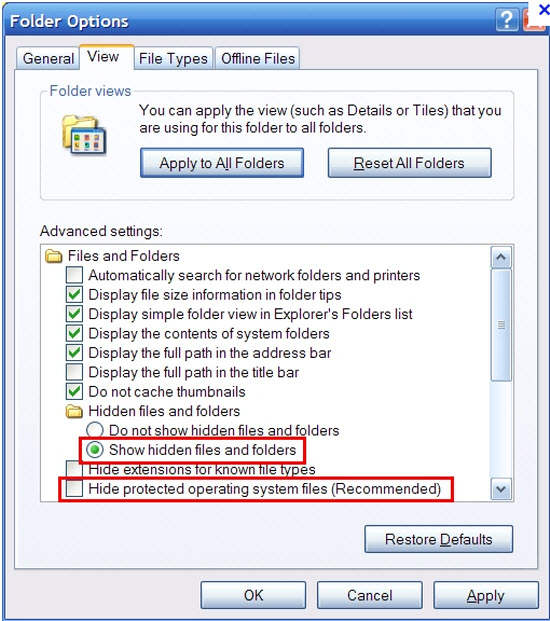
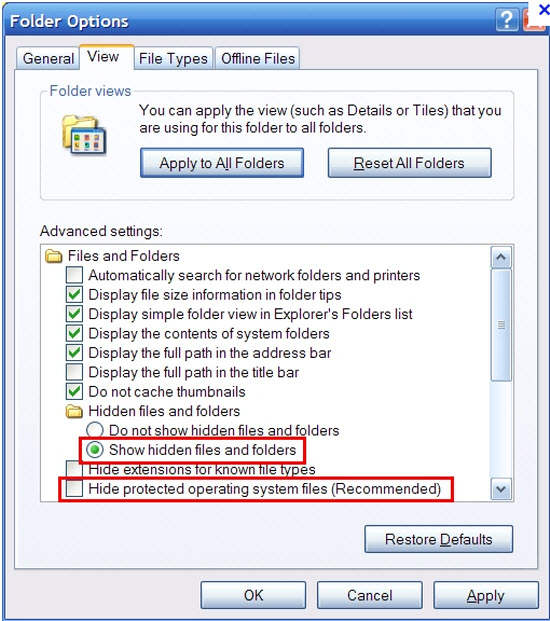
2. Show hidden files and folders.
Open Folder Options by clicking the Start button, clicking Control Panel, clicking Appearance and Personalization, and then clicking Folder Options.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
Click the View tab.
Under Advanced settings, click Show hidden files and folders, uncheck Hide protected operating system files (Recommended) and then click OK.
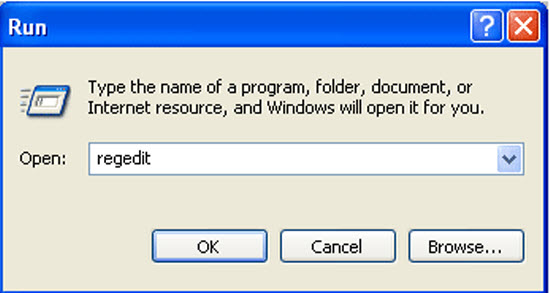
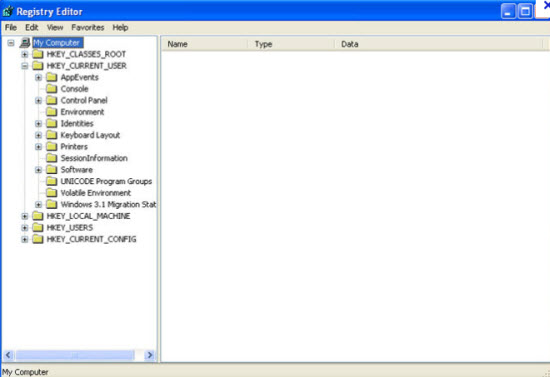
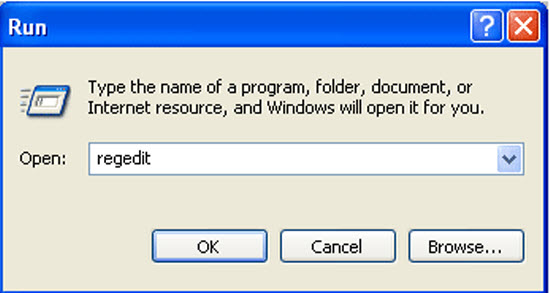
3. Open Registry entries. Find out the malicious files and entries and then delete all.
Attention: Always be sure to back up your PC before making any changes.
a. Press the “Start” button and then choose the option “Run”. In the “Open” field, type “regedit” and click the “OK” button.
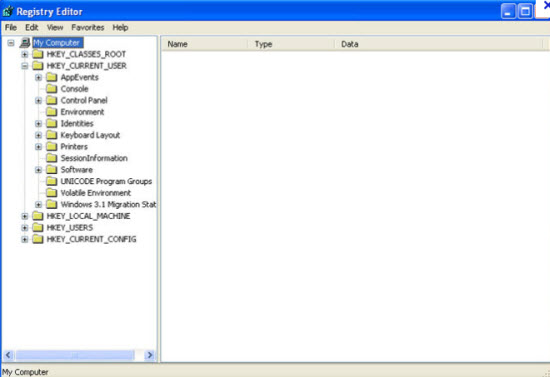
b. All malicious files and registry entries that should be deleted:
%System%\drivers\[RANDOM CHARACTERS].sys
%Temp%\[random]
C:\WINDOWS\system32\[random name].dll
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer “NoDesktop” = ’1?
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableTaskMgr” = ’1?
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “[random].exe”
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run “[random]”
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system “DisableTaskMgr” = ’1?
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download “CheckExeSignatures” = ‘no’
Video Shows You How to Safely Modify Windows Registry Editor:
Manual removal of TR/ATRAPS.Gen2 requires Expertise, Please take care before performing the steps.




![Smart HDD [Image: Smart-HDD.png]](http://malwaretips.com/images/fakeav/Smart-HDD.png)
![Safe Mode with Networking screen [Image: Safemode.jpg]](http://malwaretips.com/images/removalguide/safemode.jpg)
![Internet Options in IE [Image: Internet-options-IE.png]](http://malwaretips.com/images/removalguide/ie1.png)
![Connections tab in Internet Explorer [Image: Remove-proxy-server2.png]](http://malwaretips.com/images/removalguide/ie2.png)
![Uncheck the option Use a proxy server for your LAN [Image: Remove-proxy-server3.png]](http://malwaretips.com/images/removalguide/ie3.png)

![RKILL ICON [Image: run-rkill-1.png]](http://malwaretips.com/images/removalguide/rkill1.png)
![RKILL Command prompt [Image: run-rkill-2.png]](http://malwaretips.com/images/removalguide/rkill2.png)
![RKILL LOG [Image: Smart HDD rkill3.jpg]](http://malwaretips.com/images/removalguide/rkill3.png)
![Malwarebytes Anti-Malware Installer [Image: malwarebytes-installer.png]](http://malwaretips.com/images/removalguide/mbam1.png)
![Install Malwarebytes Anti-Malware [Image: install-malwarebytes.png]](http://malwaretips.com/images/removalguide/mbam2.png)
![Decline trial period in Malwarebytes Anti-Malware [Image: decline-trial-malwarebytes.png]](http://malwaretips.com/images/removalguide/mbam3.PNG)
![Perform a Full System Scan [Image: malwarebytes-full-system-scan.png]](http://malwaretips.com/images/removalguide/mbam4.png)
![Malwarebytes Anti-Malware scanning for Smart HDD [Image: malwarebytes-scanning.png]](http://malwaretips.com/images/removalguide/mbam5.png)
![Malwarebytes when the scan is finished [Image: malwarebytes-scan-finish.png]](http://malwaretips.com/images/removalguide/mbam9.png)
![Smart HDD infection scan results [Image: malwarebytes-scan-results.png]](http://malwaretips.com/images/removalguide/mbam6.png)
![Reboot prompt from Malwarebytes [Image: malwarebytes-reboot-prompt.png]](http://malwaretips.com/images/removalguide/mbam10.png)
![HitmanPro Installer [Image: hitmanpro-icon.png]](http://malwaretips.com/images/removalguide/hpro1.png)
![HitmanPro installation process [Image: installing-hitmanpro.png]](http://malwaretips.com/images/removalguide/hpro2.png)
![HitmanPro setup options [Image: hitmanpro-setup-options.png]](http://malwaretips.com/images/removalguide/hpro3.png)
![HitmanPro scanning for Smart HDD [Image: hitmanpro-scanning.png]](http://malwaretips.com/images/removalguide/hpro4.png)
![HitmanPro Smart HDD scan results [Image: hitmanpro-scan-results.png]](http://malwaretips.com/blogs/wp-content/uploads/2012/02/rsz_hpro5.png)
![Activate HitmanPro free license to remove detected infections [Image: hitmanpro-activation.png]](http://malwaretips.com/images/removalguide/hpro6.png)
![Click on the Start button to unhide your files [Image: unhide-icon.png]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/unhide-files.png)
![Click on the Start button to perform a system scan [Image: roguekiller-1.png]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-1.png)
![Press Delete to remove the malicious registry keys [Image: roguekiller-2.png]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-2.png)
![Click on the Start button to perform a system scan [Image: roguekiller-1.png]](http://malwaretips.com/blogs/wp-content/uploads/2012/04/roguek-3.png)
![Enable the option to see hidden files [Image: viewhiddenfiles.png]](http://malwaretips.com/images/removalguide/view-hidden-items.png)
![Show hidden files, folders, and drives [Image: Show hidden files, folders, and drives.png]](http://malwaretips.com/images/removalguide/see-hidden-files.png)
![Copy the content of each folder to their original location [Image: Show hidden files, folders, and drives.png]](http://malwaretips.com/images/removalguide/path-to-hidden-files.png)


